Data security practices are essential in onsite works but play a more prominent role in remote working. In simple terms, data security refers to how data protection is possible in all the data lifecycle stages, avoiding data breaching, unauthorized access, and theft.
Data is the new gem, so it is essential to keep track of data in remote work where the team members are scattered.
The offices should plan for better data protection and allocate a data security policy to mitigate the risks and threats to crucial data and information.
Types of Data Security in Remote Work
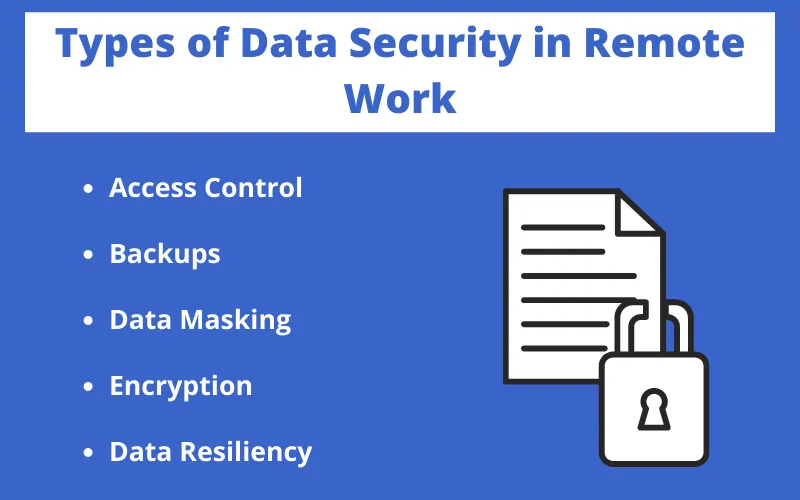
Some data security practices increase data security. The adoption of different types of protection in virtual offices assures safety to organizational data.
Every remote worker must know the data used as resources or generated via an organization’s other tools and software.
Access Control
Data security practices include access control in which the authority for sensitive data is allowed only to certain people. In remote work, the office members can access data hierarchically and work-wise.
Access control is vital for safeguarding sensitive data. One of the key benefits of access reviews is that they allow organizations to regularly assess and manage who has access to what data. This helps in maintaining data integrity and confidentiality, mitigating the risks associated with data breaches, especially in remote work environments.
Backups
When some files or documents are misplaced online, you cannot afford to lose them permanently. So the habit of keeping backups is a good one for data security.
By chance, if the data are missing, then you can always rely on the backup data and information of documents, content, research, and customer information.
Using cloud technology is the best way for workers to work from home and in different locations. The cloud security is boosted with encryption and has cloud firewalls for preventing external attacks, and there is identity and access management.
Data Masking
The organizational data are extensive in number and are the critical factors for analysis and strategy building.
Data masking is a technique that uses unreal data drafts as real ones, but in reality, the actual data are hidden or masked.
Data masking is a good idea for securing essential business data. The information on the corporate world for training purposes uses fake data.
In software testing, the simulated data used for checking functionalities and detecting errors are not actual.
Encryption
Encryption is a standard method of communication in which one form of data conversion is possible to another format. With access to the security key, the sender and receiver can get the required information.
In remote work, encryption plays a vital role as it’s used in daily chatting or sending emails to exchange documents.
The idea of protecting documents and files with a password is handy in remote work, as all transitions and outcomes occur online.
Data Resiliency
Data resiliency is essential in remote work as it offers resilience when data in one location is inaccessible while the same data is available somewhere else. Cloud technology provides data resilience.
Some Data Security Practices for Remote Workers
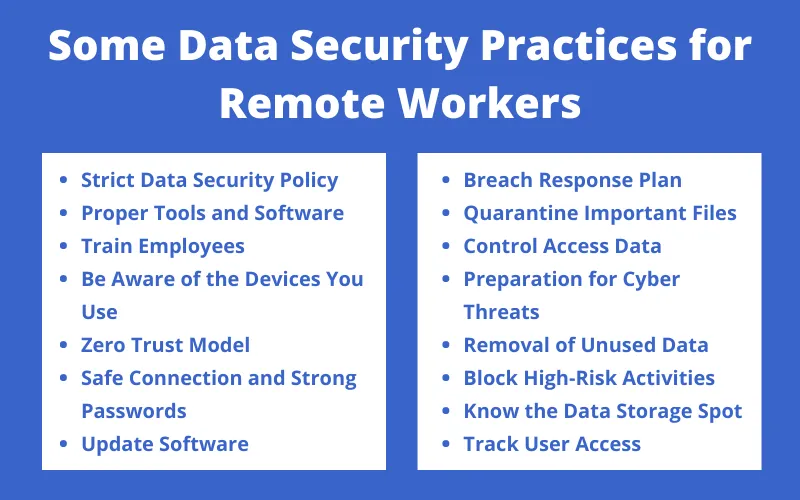
Remote work demands extra precautions and has a more significant threat to data. To avoid data disasters, users can adopt ways to keep data safe. The team members need ideas about security policies and preventing a data breach.
Strict Data Security Policy
The data security policy includes how the customer’s data and information handling occur and how the sensitive data are kept safe.
Data security policy has a procedure for data classification, password policy, encryption policy with data loss protection policy.
The employees need to learn how to handle the crucial data not to be lost or reach unauthorized people.
When every member knows clearly about the data security policy in remote work, the data is secure. The office can provide a policy list to employees to not violate any rules working from far.
Proper Tools and Software
In remote work, there is a need for specific tools and software to ensure the security of data and ease of work.
The policies for data security demand particular tools for implementing remote work among team members.
Actions for network security and installing antivirus software on devices used to work from home are some ways to ensure data safety.
Data security is high when a company makes it compulsory to use tools and software. The correct choice of software helps secure the information, and such applications keep employees alert to remember the importance of data confidentiality.
Train Employees
With modern solutions to protect data online, employees need training regarding the software and tools and every action they perform during work hours. In lack of activities and proper briefing, the employees forget to protect data online.
For awareness among workers, online seminars and programs help adequately maintain data privacy and how data needs handling with security best practices.
Be Aware of the Devices You Use
The use of personal devices during work is not a good idea. The company is supposed to provide the workers with secure devices to perform the necessary tasks. Laptops issued by offices have tools to protect data.
There are high chances of data breaches when you use your device or someone else’s device at home for work.
Zero Trust Model
This model is based on the recommendation for access control. When you have to share resources with members, the Microsoft zero trust model simplifies the process by reminding the access granter to check the identity and device before allowing access.
If the same strategy adoption occurs in remote work, trust is absent in each employee regarding data security. There is validation monitoring at every step of data exchange or digital transaction.
Safe Connection and Strong Passwords
The only way to connect to team members working from different places is via the internet. When the connection is not secure, the users are victims of cybercrimes like DDOS (Distributed Denial Of Services) Attacks. This situation calls for the use of a VPN for office work.
There are certain conditions for VPN like server network, firewalls for managing traffic, and enabling secure connections for work.
Strong passwords for individual accounts are essential and use safe password managers to remember passwords.
Update Software
The regular updating of software on personal or official devices is mandatory. Every software has its security updates and versions with patches and provides security. Conducting pen tests is also a good idea.
Updated software works faster, and the delayed patches help reduce the vulnerability of the devices with better security plans.
Breach Response Plan
The breach response plan is drafted as planning when a data breach occurs. If you have a breach response plan, there is no need to panic if a data breach happens during remote access.
Strategic planning has a list of actions to perform right after a breach. But the best is adopting ways so that violations never take place.
Quarantine Important Files
Not all files hold the same level of importance. The members need to differentiate between the most essential and least essential data.
After distinguishing between the data types, make a separate place for the crucial data.
When you mix the most essential and least essential data, you may end up sharing the most critical data with people who have no authority over it via network access.
Control Access Data
The administrative control on data includes educating employees, and technical control allows partial or complete control over data with the right to modification and reading or reading only. An application has its access control list.
The security and devices have DLP (Data Loss Prevention) and Firewalls with NAC (Network Access Control).
Preparation for Cyber Threats
By using the internet, cyber threats may arrive in any form. The best way to deal with cyber threats is to implement when a cyber threat occurs and protect your data.
Cyber security policy plays a vital role in defining the actions in cyber threats. With the tracking software, you can detect unwanted activities from third parties outside the office, reducing internal threats.
Removal of Unused Data
After using the data to the fullest, it is not safe to keep them. The stale data needs removal as hackers may eye on the data, so it’s better to delete them permanently.
Users should remember to delete every location of the same data when it’s not essential. For a more secure and efficient data removal process, consider utilizing a data removal service. This can help ensure that all data traces are erased, minimizing the risk of exposure and cyberattacks.
Block High-Risk Activities
With the right software installed on your system, blocking risky activities is possible. The software can detect actions that make it stop activities that seem dangerous for the device’s security.
A typical example is sharing important passwords or data without encryption. When the software in your device finds that the data needing encryption is not encrypted, it takes action by blocking the activity to protect the device to ensure data security. This level of proactive security is made possible through machine learning bot detection software, which continuously analyzes data patterns and behavior to identify potential threats and vulnerabilities.
Know the Data Storage Spot
In having a large amount of data for storage, you forget which data resides. You must create a list of reminders or use a management system for maintaining the company’s data.
It is easier to use and access data by detecting which location has what data and even providing resources for users who require data.
Track User Access
Only the people who are allowed to access data do not seek it. For users who wish to get data not authorized to them, the constant tacking of user access is essential to maintain the confidentiality of the data.
Some Other Strategies for Data Security

There are other things to remember when data security is the concern. The strategies are the procedures and technology that require continuing in the office. Some different techniques for keeping the data safe in online working are:
Security of Devices and Servers Physically
The central office has different servers in remote work, and the servers used for office work are in other locations. Generally, data is secure virtually, but servers and computers also require safety from attackers.
Offices need to lock in essential devices and servers to ensure data safety and security. The presence of security guards and robust security is necessary.
You can install antivirus software on your device with two-factor authentication as a practice to ensure password safety.
Network Monitoring Tools
The only way to connect with remote team members at work from home is via the internet. The attacks also appear from the internet, so it’s necessary to monitor your network continuously.
Network monitoring tools check the different networks to ensure the connection situation.
Some Common Mistakes Done By Remote Workers
Remote employees need to take care of the official files and handle them properly. Knowing and unknowingly, there are certain things remote workers may end up doing and need to avoid for better data security. Additionally, incorporating residential proxy servers can further enhance security by providing IP addresses from residential networks, adding an extra layer of protection against potential threats.
Some common mistakes done by workers working away from onsite offices are:
- Employees upload the official files to their email or cloud accounts by mistake and even use personal emails for communication.
- When the official accounts demand a password change, the office members use the same password after each renewal duration.
- Some employees try to access data that is not authorized for them, which creates a problem.
- After the onboarding process, only a few companies provide briefings to the new employees regarding data security policy.
- Employees in remote work share their passwords with other members and forget to delete files after use.
- The use of the same password on different accounts is bad practice.
- Mixing up personal and office devices results in data and official information threats.
- Taking official devices while traveling and leaving the PC unattended by improperly closing the device adds insecurity to data.
- After quitting jobs, some ex-employees still access data and do not remove the previous official files and documents.
- Sometimes the team lead or manager mistakes gives access to individuals who should not access the data.
Cyber Attacks and Remote Team’s Data
The attackers are eager to find remote teams that work with confidential data. Attackers use different methods like sending ransomware threats to scare employees and ask for data from the office.
Phishing scams include filling up forms with your data, and some employees are victims of severe fake data breaches.
Deep-fake data breaches are possible when attackers appear as someone with whom you had scheduled a meeting and ended up retrieving important information.
Conclusion
Cybersecurity awareness is vital for remote employees to ensure data security online. The company’s data is in employees’ hands, and security best practices include password managers and not using personal devices for work. Remote access is possible via the virtual private network VPN.



 Employee Screen Monitoring Software
Employee Screen Monitoring Software App and Website Monitoring Software
App and Website Monitoring Software Time and Attendance Software
Time and Attendance Software Finance
Finance Banking
Banking Healthcare
Healthcare Lawyers
Lawyers Retail & ecommerce
Retail & ecommerce Knowledge base
Knowledge base Blogs
Blogs Installation Guide
Installation Guide FAQs
FAQs About
About Media Kit
Media Kit Contact us
Contact us